Single sign-on configuration
Single sign-on (SSO) allows users to log in to Amplience using their organization's identity provider and without having to have an Amplience specific user name and password. You can use your own identity provider and the credentials you already have.
SSO provides many benefits, including:
- Users can switch between different Amplience apps easily, without the need to log in to each app.
- You use your existing credentials and do not need a new user name and password for Amplience.
- For an organization it provides more control over who has access to the systems they use. For example, if someone leaves an organization and is removed from their identity provider platform, then they can no longer log in.
- You can also take advantage of multi factor authentication and the password complexity and password expiry settings implemented by your identity provider.
SSO login processLink copied!
When using SSO, the login process will be as follows:
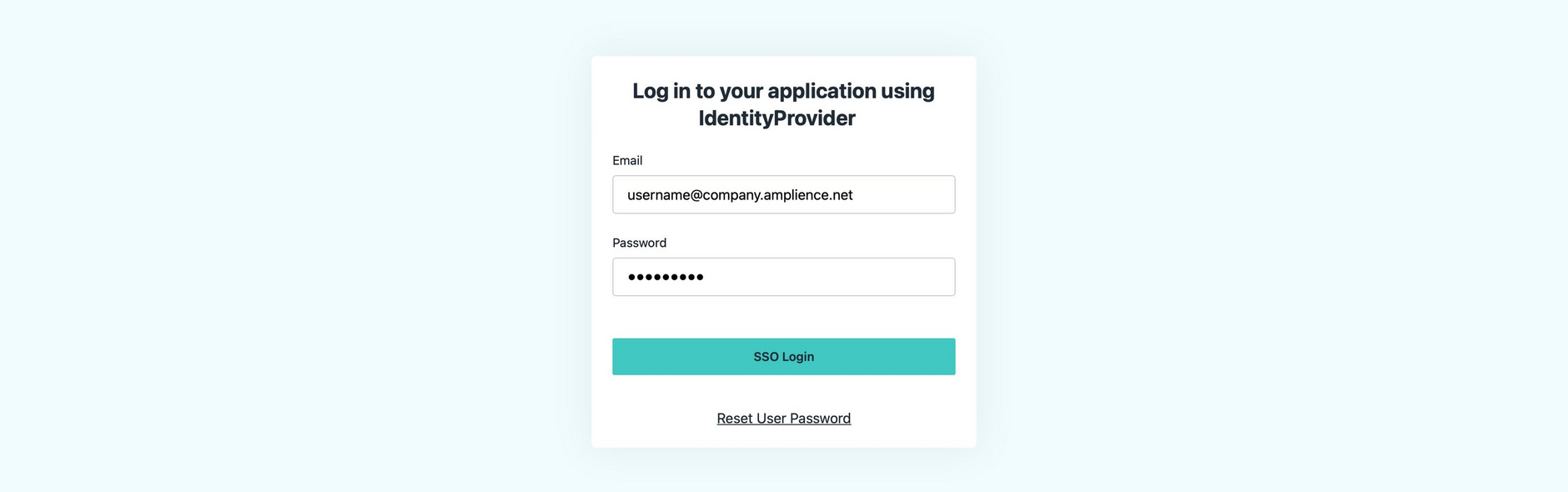
- The user visits the Amplience single sign-on page for their organization and clicks the "Log in" button.
- The user is redirected to the single sign-on page of the identity provider configured for their organization and enters their usual name and password.
- Note, if the user has logged out, (or been logged out automatically) they will be prompted to login again (and will need to choose the SSO login option on the login screen).
- The identity provider then authenticates the user and sends a "claim" to the Amplience authentication service. This will include the user's email address.
- Amplience will then check that the user is allowed access and if so logs the user in. If the user has not been set up for access to Amplience, then an error will be displayed.
User accounts are automatically created when new single sign-on users log in to Amplience. Their roles will be depend on how you've configured onboarding teams and claims within your identity provider. For more information see Adding a user.
Identity providersLink copied!
Amplience single sign-on supports most enterprise identity providers, including (but not limited to) the following:
Almost all of the identity providers use Security Assertion Markup Language (SAML) or OpenID Connect authentication protocol (OIDC), as the authentication protocol to communicate between the identity provider and the service provider, which in this case will be Amplience.
The authentication protocol you use will determine how Amplience will be configured with your identity provider. In all cases we will provide you with some information to set up Amplience with your identity provider, while you will provide us with information to authenticate your users. Some identity providers support both SAML and OIDC and in this case the protocol you choose will depend on your information security requirements.
Configuring an identity provider using SAMLLink copied!
To configure SSO with SAML you will need to do the following:
- Tell Amplience the domain you wish to use as part of your login URL:
- Provide Amplience with the login URL. This is the identity provider URL to which the user will be redirected when they login from the Amplience SSO landing page.
Set up an app in your identity providerLink copied!
The app you create in the identity provider will need to be configured with SAML metadata, including the following information provided to you by Amplience:
- Assertion customer service URL.
This is the URL of the Amplience API endpoint where the identity provider should send the authenticated user's data.
- EntityID.
This URI is a unique identifier used for the connection between Amplience and the identity provider.
X.509 certificatesLink copied!
Requests and responses between Amplience and your identity provider are signed using X.509 certificates. We will send you the Amplience X.509 certificate and you need to send us your identity provider's X.509 certificate. Using certificates ensures that requests and responses can be verified as originating from Amplience or the identity provider, and that the data has not been modified in transit.
Unique user identifier (nameID)Link copied!
You need to configure additional SAML attributes that are used to identify the user. These attributes should include:
| Attribute | Notes |
|---|---|
nameID | This is the unique identifier for the user. We require that the user's email address is sent as the unique identifier. nameID is a required attribute. |
name | The name that is shown in the user list in Account Management. name must be lowercase |
email | The user's email must also be specified in this attribute. We use the email to determine which Amplience account to use. email must be lowercase |
All the above is specified in XML format.
Configuring an identity provider using OIDCLink copied!
To configure SSO with an OIDC identity provider you will need to do the following:
Tell Amplience the domain you wish to use as part of your login URL:
Provide Amplience with the login URL. This is the identity provider URL to which the user should be redirected when they log in from the Amplience SSO landing page.
Set up an app in your identity provider. As part of this process you will generate a key and secret which should be sent to Amplience in a secure manner.
Configuring permissions via SSOLink copied!
You can configure SSO to apply permissions for Dynamic Content users as they log in, if your identity provider allows. To do this you use SSO claims and attributes.
Once configured, users will automatically get permissions from teams in Account Management.
Onboarding teams can be used to automatically provide permissions for SSO users as they log in. See Onboarding teams
Here's a general guide of how to apply user account permissions through SSO.
Before you start configuration for permissions in your identity provider, you will need at least one team in Account Management that has appropriate permissions for new user accounts. See Creating teams.
For this example, we already have some teams set up in Account Management.
Ensure that the app setup in your identity provider includes the ampTeams attribute. You may have already done this when initially configuring your identity provider.
Depending on your identify provider, you might set up a claim (or group claim) that includes an attribute with the name ampTeams.
Here's an example of the ampTeams attribute in the JumpCloud identity provider:
Next, within your identity provider add teams or user groups with names that exactly match the team names that you want to use in Account Management. Then add users to these teams or groups.
In this example, we've added some teams to our JumpCloud "User Groups". The team names match teams we have in Account Management. Users who will log in through SSO can be added to these teams.
When users log in to Amplience, the ampTeams attribute will be used to check which teams or groups those users have been added to within your identity provider. The identity provider team is then used to add users to the corresponding teams in Account Management to set their permissions.
Adding a userLink copied!
User accounts are automatically created when new single sign-on users log in to Amplience.
Users must be granted permissions before they can use the Amplience platform.
For Dynamic Content users, permissions can be automatically applied at log in if you've configured SSO claims within your identity provider. You will need to add any new users to the relevant teams or groups set up in your identify provider.
Other ways you can set permissions for Dynamic Content user accounts are:
- Users with organization or hub admin roles can set Dynamic Content permissions through Account Management. See setting permissions.
- Onboarding teams can be used to provide initial permissions instead of setting them through invites or SSO. See Assigning initial permissions.
Note, if Dynamic Content users require permission to access assets stores and assets through the Assets tab, you'll need to request Assets tab provisioning.
To set Content Hub permissions, please raise a request through Amplience Support or contact your Customer Success Manager.